
The ruling party in Israel in primaries election security blunder
This is an amazing story about how security issues can inflict damage even on old fashioned paper ballot elections.
The Likud is Israel's ruling parties for a couple of years. This is the party of Benjamin Netanyahu, Israel's prime minister. The Likud's primaries election were held on February 4, Those elections were old fashion - means no voting machines, no web system. Just old, plain, paper ballot thrown to a box. You know the drill.
After the elections, there were some miscalculations, issues, and highly suspicious results. The prime minister ordered recounting of the vote.
The recounting process is also made by hand, but someone needs to count those ballots and after counting the results should be written and aggregated in a computer. This how things are done, we collect the data by hand but write it down in a computer system.
In the middle of the process, one of the reporters got her hand on a picture of the system with the unofficial results.
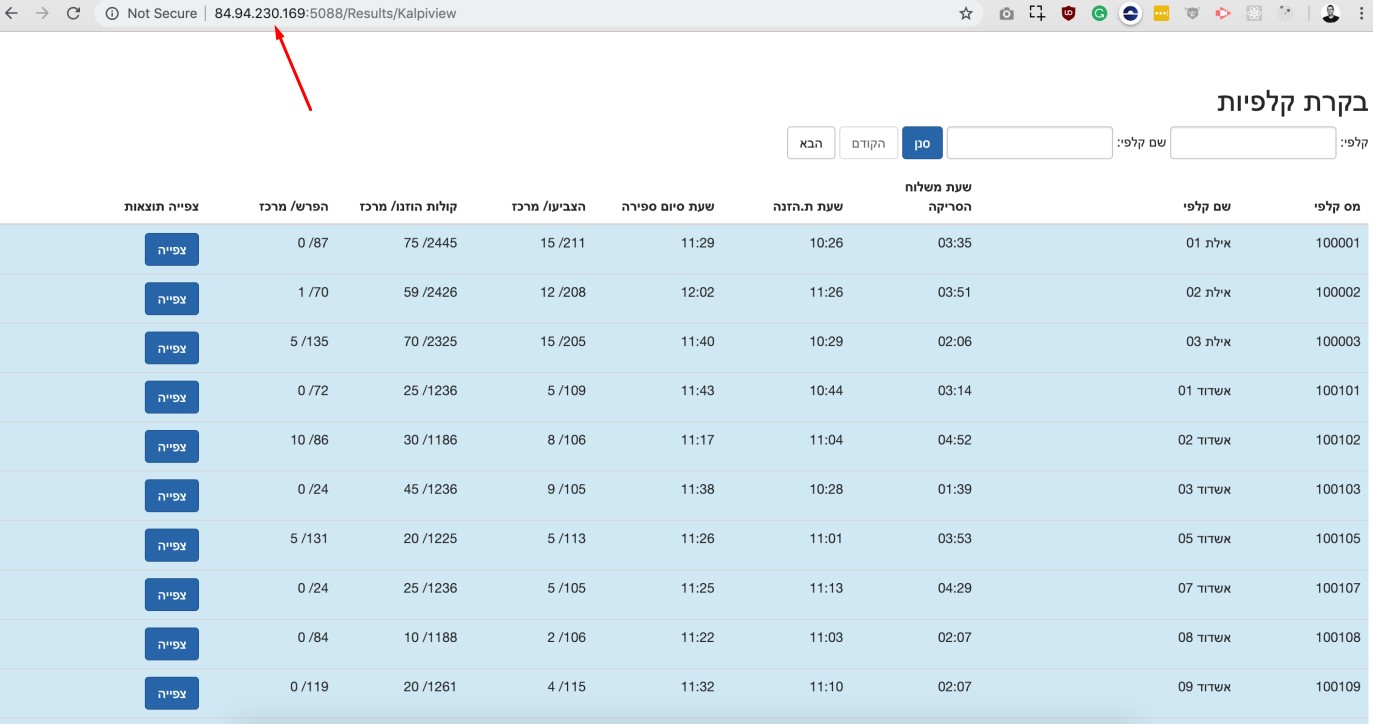
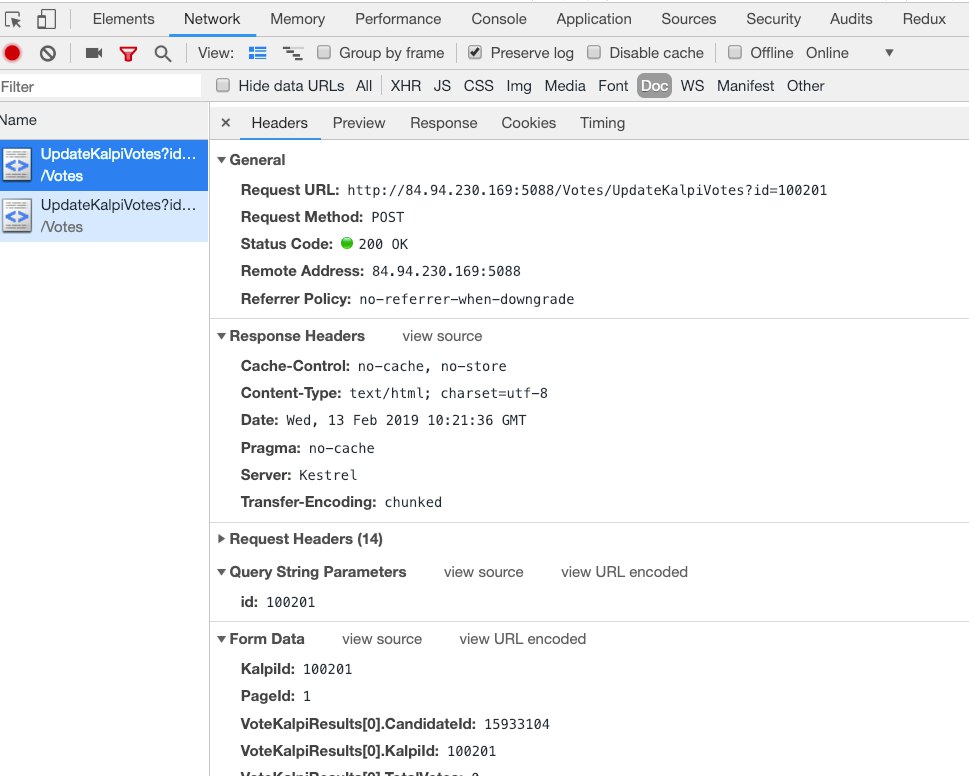
Twitter snapshot, the text says that the recounting is in the process and you can see that the voting is different from the initial count. If you will look closely, you will see that the IP address is visible. I and other Twitter users tried to put this IP in our browsers and… I was surprised to find out that I have full access to the entire recounting system.
Full access to the results FULL access, that's right - not just viewing permission but also access to the editing interface - it means that I could change the recounting results freely.
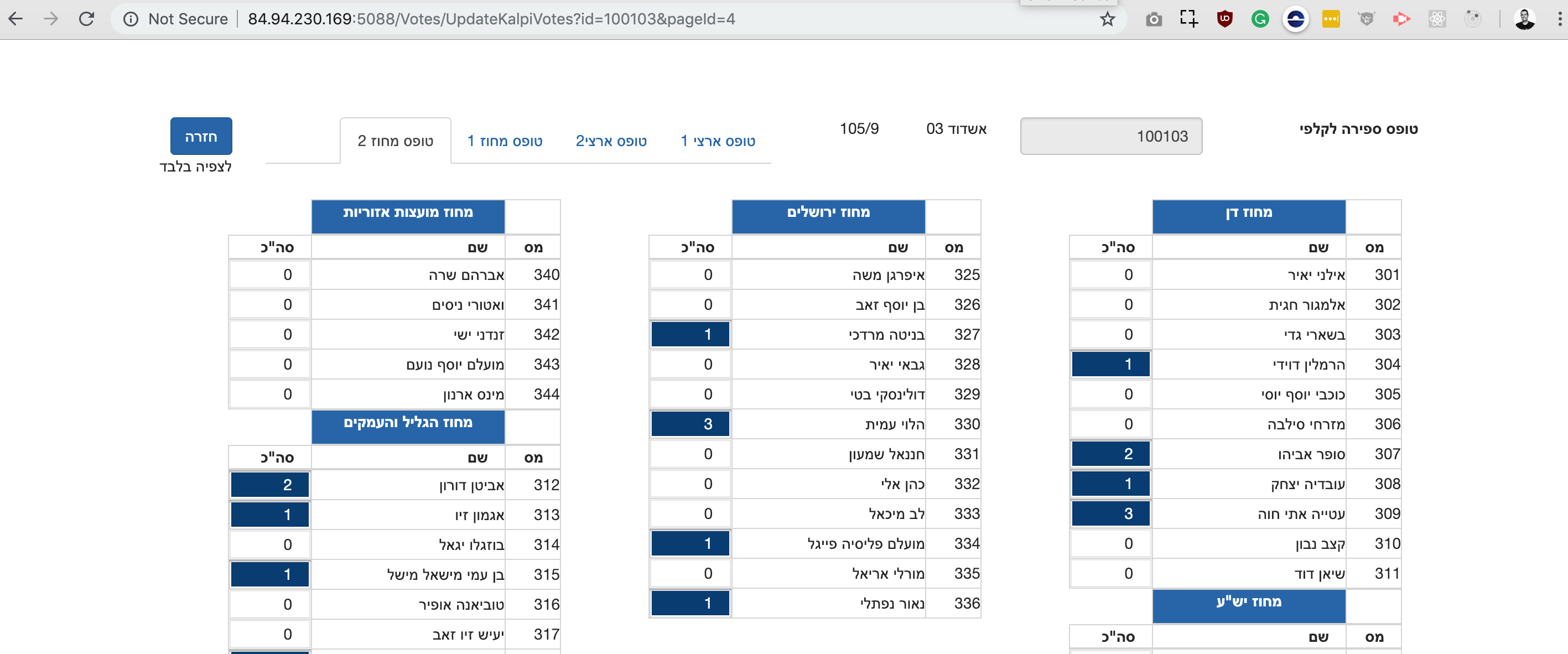
Editing interface - fully functional. That's correct, ladies and gentlemen! The system's software engineers made the rather questionable decision of not implementing any access control measures. Consequently, anyone who knew the IP address of the system - and there were numerous individuals in possession of this information - had the ability to manipulate the voting results.
If even simple access control measures were not installed, what else went wrong in that system? in other systems? Can we believe that no one exploited the recounting process? Does this system was used in the previous counting?
This recounting process is contaminated. The Likud party must hire an external security professional to validate the recounting process.
