
Petya Ransomware Attack: What You Need to Know
The latest cyber onslaught, known as Petya, emerged nearly two days ago on June 27. Identified as a ransomware attack, it encrypts the appropriated data until a ransom in BitCoin is remitted. Petya has successfully breached thousands of targets across nations such as Ukraine, Russia, India, and the U.S.
The ransomware uses the same Microsoft EternalBlue exploit that made the WannaCry attack so viral back in May. WannaCry spread to hundreds of thousands of Microsoft computers, and it seems that many Microsoft users still have not updated their systems with the patch. But whereas WannaCry spread like wildfire, Petya is unfurling at a much slower rate. However, the new ransomware makes up for it with an updated system. One of WannaCry’s spectacular errors was its built-in kill-switch, but researchers have yet to find one in Petya.
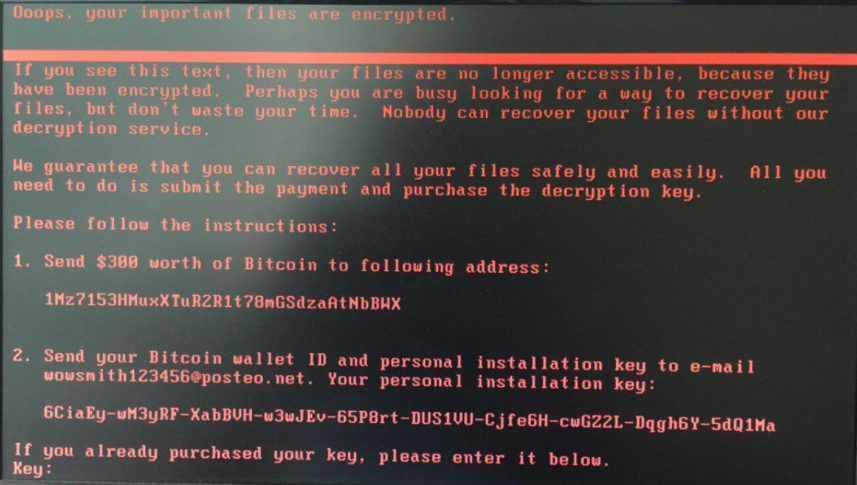
In order not to confuse it with a similar ransomware code from 2016, many are calling the virus NotPetya or GoldenEye. Whatever name you call it, the ransomware seems to use an LSADump, according to Russian security firm Group-IB, that gathers passwords and data from Windows computers and attack others on a shared network. Researchers believe the virus was seeded through a software update mechanism in MeDoc, an accounting program that companies working with the Ukrainian government use. This is probably why Ukraine has been hit the hardest, especially their government, local banks, and big companies. And while companies all over the world scramble to pay the $300, recent analysis shows that the ransomware might actually be destructive cyber malware. Researchers noted two oddities in Petya that don’t usually occur with other ransomware: the malware message urges victims to communicate via email instead of Tor, and it only lists one BitCoin address instead of an individual one for each victim. Both of these unusual elements are causing researchers to speculate that the stolen data is not encrypted but rather has been destroyed.
Even if this isn’t true, the email address that victims were supposed to communicate with was suspended, so there’s hardly any hope for retrieving those lost files even if victims pay the ransom.
The good news is that researchers found a way to stop the virus. Once infected, the ransomware waits about an hour before rebooting. Turning off the machine while rebooting will prevent files from being encrypted.
If you haven't updated your Microsoft Windows with the patch, now is the time.

